Reporting a security issue
Found a security issue with Mautic or an officially supported plugin? Read on for how to responsibly disclose it to the Security Team.
Submitting an issue
If you discover or learn about a potential error, weakness, or threat that can compromise the security of Mautic and is covered by the Security Advisory Policy, we ask you to keep it confidential and submit your concern to the Mautic security team.
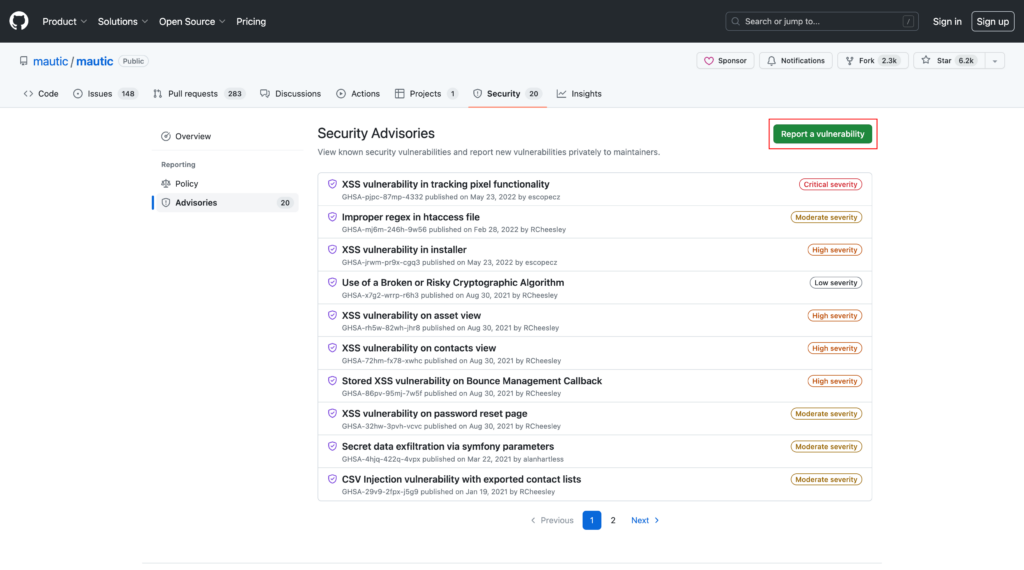
To make your report please submit it as a private disclosure at https://github.com/mautic/mautic/security. Please only create one security advisory for one issue. If you’ve found multiple, create one for each thing you’ve found.
You can also create a private fork once the advisory is created to provide a fix, if you’re able to do so. See the documentation from GitHub on privately reporting a security issue.
Do not post it in Github as a regular issue or a pull request, on the forums, or or discuss it in Slack.
The security team will investigate your report and then work with you and the Product Team to create a fix. If the fix is ready, we will create a release and announce the fix to a wide audience.
Some bugs take time to correct and the process may involve a review of the codebase for similar problems. Coordinating across time zones and work schedules can be time-consuming. We aim to fix issues within 1 month, but we also need to balance that with the available time of our volunteer team and the need to release high quality fixes.
Do not disclose the vulnerability to anyone else before the advisory is issued.
If the vulnerability is not covered by the Security advisory policy, you can still report it via these channels, but it’s also acceptable to post it directly to Github.
How to make a good security report
Provide a detailed report. Each field in the form contains helpful information, please ensure you complete them all.
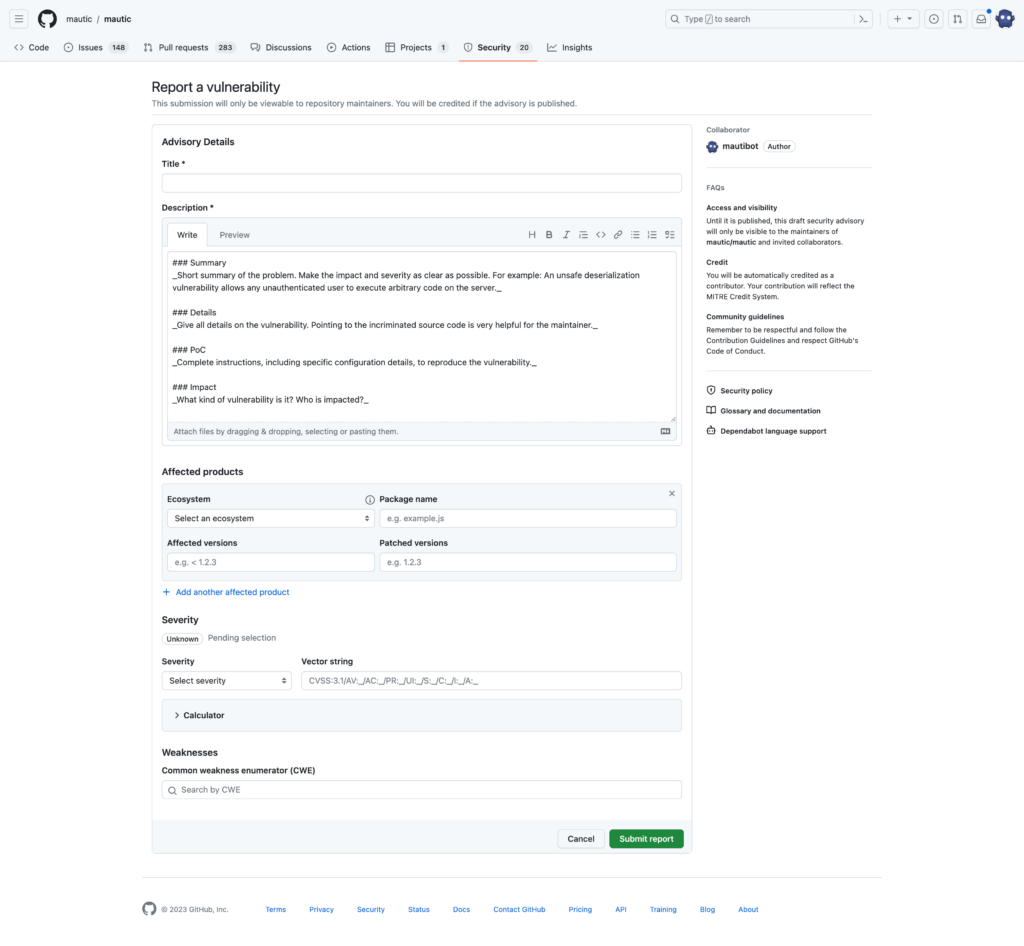
Use the following:
- Ecosystem: Composer
- Package name: Mautic (or plugin/package name as appropriate)
- Affected versions: Please provide versions where this issue is present, ideally when it was first introduced in the code – if you don’t know, the Security Team will add this. You should test the current stable and development versions. See https://mau.tc/tester for details on how to spin up an instance on Gitpod for testing.
- Patched version: Leave this field blank
- Severity: Please use the calculator to create the CVSS scoring value which will be confirmed by the Security Team. More information on what each value means can be found in the CVSS user guide.
- Weakness: Please choose the most appropriate CWE type which will be confirmed by the Security Team. Read more about the types on the Mitre CWE database.
Include in your description as many of these items as possible:
- Short summary of the issue: A one-liner which explains what the vulnerability is about
- Full details of the issue: Include code snippets where possible to provide deeper information.
- Steps to reproduce the problem: Explain how to reproduce this issue when starting from a fresh install. Ensure you cover both the current stable and development versions.
- Impact of the vulnerability.
- A proposed fix or way of addressing the vulnerability, if possible. Once you submit the report you can make a private fork and submit the vulnerability fix if you’re able to do this – please make a separate PR for each branch of Mautic which is currently in active or security support and which is affected by the vulnerability.
- Workarounds: are there any ways people can work around the vulnerability? Is there anything that can be done at the server-level to mitigate against abuse
- Resources: if sharing a vulnerability reported elsewhere, or there are links to similar vulnerabilities or other relevant resources, please include these in your report
Optional: you can indicate the way you would like to be referred to in the advisory about the vulnerability. Our preference is to credit people using full names and where appropriate an organisation when we are announcing a security fix, but at minimum your GitHub account will be mentioned. If you do not specify we will do our best to find that information. You can also request a pseudonym or having your name withheld.
The Mautic Security Team does not disclose proof-of-concept information to demonstrate vulnerabilities and reporters are encouraged to do the same.
Where a reporter feels strongly that proof-of-concept instructions should be published, they are encouraged to hold that information for an additional period of at least 4 weeks after the release of the patched version of the software.
What if the vulnerability affects a plugin which isn't covered by the Security Advisory Policy?
If you are absolutely sure that the plugin is not covered by the official Mautic security policy, you should report the issue through the security policy processes of the plugin, If one isn’t published but there’s a contact address use that, otherwise as a last resort, post a general non-specific issue explaining you’ve found a security issue and need to know who to contact.
It is considered good form to copy in the [email protected] email list if possible when reporting issues with third party plugins so that the Security Team is aware, but the Mautic Security Team does not handle security advisories for plugins hosted elsewhere.